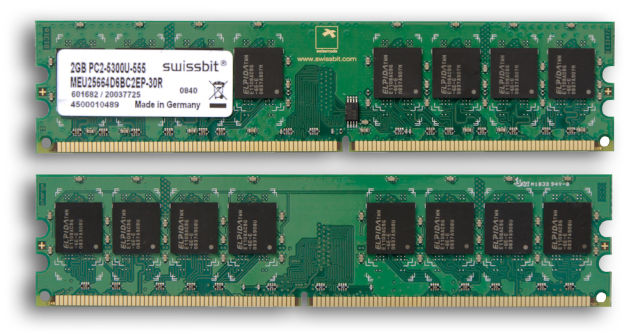
(credit: An-d)
New research into the "Rowhammer" bug that resides in certain types of DDR memory chips raises a troubling new prospect: attacks that use Web applications or booby-trapped videos and documents to trigger so-called bitflipping exploits that allow hackers to take control of vulnerable computers.
The scenario is based on a finding that the Rowhammer vulnerability can be triggered by what's known as non-temporal code instructions. That opens vulnerable machines to several types of exploits that haven't been discussed in previous research papers. For instance, malicious Web applications could use non-temporal code to cause code to break out of browser security sandboxes and access sensitive parts of an operating system. Another example: attackers could take advantage of media players, file readers, file compression utilities, or other apps already installed on Rowhammer-susceptible machines and cause the apps to trigger the attacks.
As Ars has previously reported, Rowhammer exploits physical weaknesses in certain types of DDR memory chips to reverse the individual bits of data they store. By repeatedly accessing small regions of memory many times per second, code can change zeroes to ones and vice versa in adjacent regions. These changes occur even though the exploit code doesn't access, and doesn't have access rights to, the adjacent regions. The bug took on the name Rowhammer, because when the code figuratively clobbers one or more rows of memory cells, it causes bitflips in a neighboring cell.