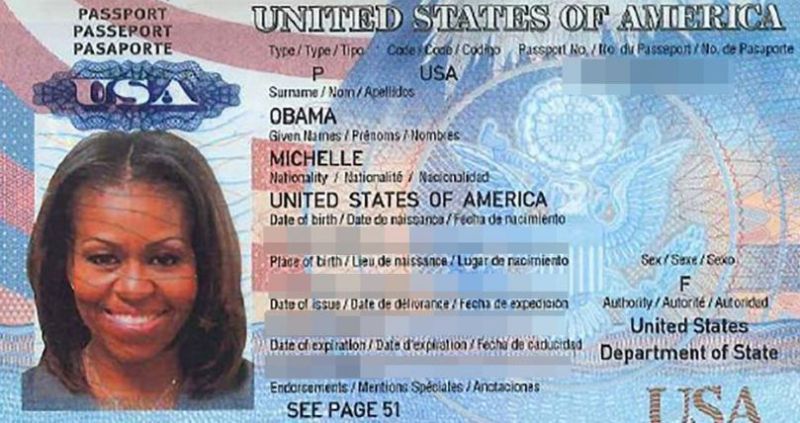
Enlarge / A photo of First Lady Michelle Obama's passport from a dump of the e-mail of White House contractor Ian Mellul. Mellul's password may have been in a 2013 Adobe user data breach.
On September 21, a dump of an e-mail account belonging to a White House contractor was posted to the "hacktivist" website DCleaks.com. This is the same site that already revealed e-mails from former Secretary of State Colin Powell, a Navy captain leading a weapons procurement program, and a public relations person who has done advance work for Hillary Clinton. The latest victim did advance work for travel by First Lady Michelle Obama and Vice President Joe Biden. Attributing the leak will be difficult because, as with previous "dumps" published on DCleaks, the compromised account's password information was widely available on the Internet from a previous data breach.
An unnamed US intelligence official was quoted by NBC News as calling the leak of contractor Ian Mellul's e-mails "the most damaging compromise of the security of the president of the United States that I've seen in decades"—one caused by the use of an outside personal e-mail account for government business. The e-mails included full scans Mellul had forwarded to himself from a White House e-mail account of passports, including Michelle Obama's. Mellul likely forwarded the e-mails to his Gmail account because he couldn't access White House mail offsite without a secure device.
Government sources have described DCleaks.com as being connected to Russian intelligence organizations. But just about anyone could have gotten into Ian Mellul's e-mail if he was using the same password for his Gmail account that was exposed in a 2013 breach of Adobe user data—just as was Navy Captain Carl Pistole's. The accounts of Powell and of Sarah Hamilton were both leaked as part of a 2012 breach of Dropbox's user data, according to data from HaveIBeenPwned.