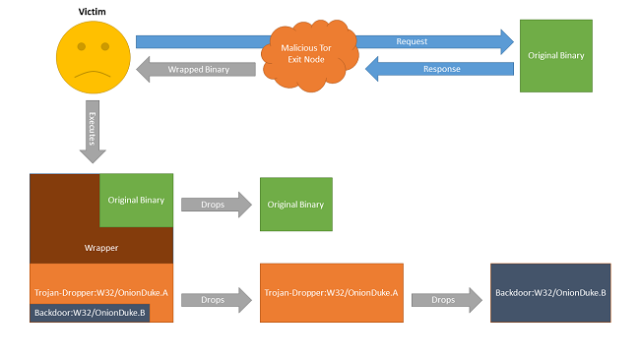
Three weeks ago, a security researcher uncovered a Tor exit node that added malware to uncompressed Windows executables passing through it. Officials with the privacy service promptly shut down the Russia-based node, but according to new research, the group behind the node had likely been infecting files for more than a year by that time, causing careless users to install a backdoor that gave attackers full control of their systems.
What's more, according to a blog post published Friday by researchers from antivirus provider F-Secure, the rogue exit node was tied to the "MiniDuke" gang, which previously infected government agencies and organizations in 23 countries with highly advanced malware that uses low-level code to stay hidden. MiniDuke was intriguing because it bore the hallmark of viruses first encountered in the mid-1990s, when shadowy groups such as 29A engineered innovative pieces of malware for fun and then documented them in an E-zine of the same name. Written in assembly language, most MiniDuke files were tiny. Their use of multiple levels of encryption and clever coding tricks made the malware hard to detect and difficult to reverse engineer. The code also contained references to Dante Alighieri's Divine Comedy and alluded to 666, the "mark of the beast" discussed in the biblical Book of Revelation.
"OnionDuke," as the malware spread through the latest attacks is known, is a completely different malware family, but some of the command and control (C&C) channels it uses to funnel commands and stolen data to and from infected machines were registered by the same persona that obtained MiniDuke C&Cs. The main component of the malware monitored several attacker-operated servers to await instructions to install other pieces of malware. Other components siphoned login credentials and system information from infected machines.
Read 3 remaining paragraphs | Comments